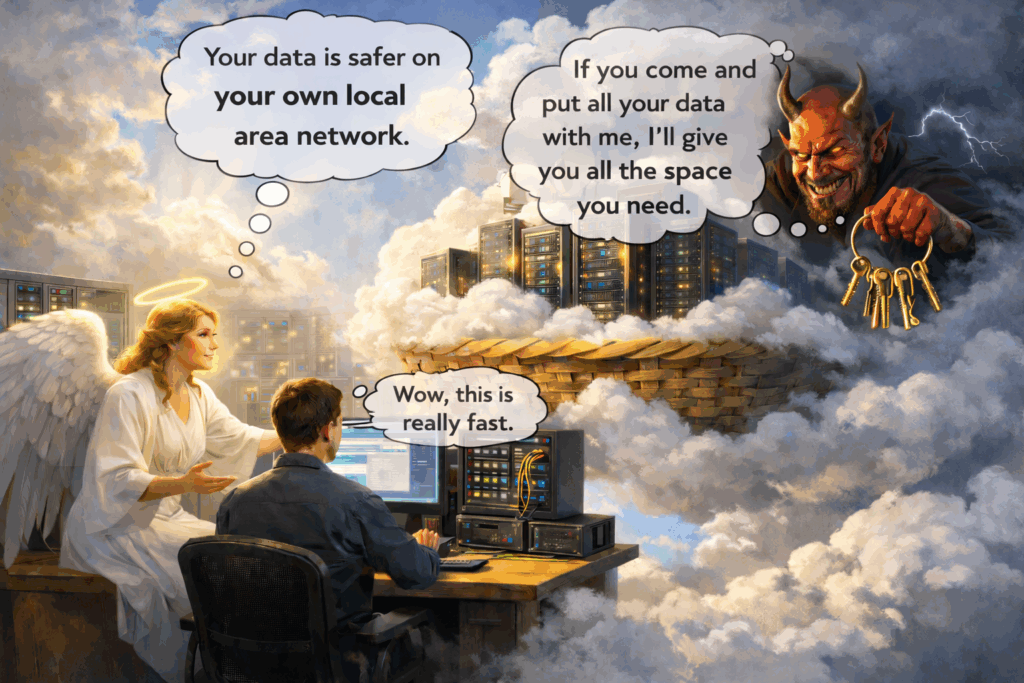
When you move your data from your building into someone else’s servers, you don’t automatically make it safer. What you often do is congregate it—along with everyone else’s data—into a handful of giant, well-known targets, and now the bad guys don’t have to hunt for you. They already know where the pile is.
It’s the “all your eggs in one basket” problem except the basket is labeled, mapped, and scanned 24/7 – 365 days a year – by thousands of bad guys. The network admins have to be right everyday about configurations and security protocols – However the bad guys only have to be right one time to make off with terabytes of data.
Cloud can absolutely be part of a good strategy. However, if your entire strategy is “it’s in the cloud,” you don’t have a strategy—you have a co-dependency. Cloud can be a tool, but if your “plan” is basically to outsource responsibility and call it resilience, that’s not a plan—it’s hope with a monthly invoice attached.
Microsoft will tell you it’s a shared-responsibility relationship: they secure their layer, you secure yours. The catch is that “your layer” is identity, permissions, conditional access, device posture, sharing controls, retention. Those settings are complicated enough that most businesses don’t realize what they missed until after the incident.
Treat the cloud like a silver bullet and sooner or later the odds catch up—maybe it’s an outage, maybe it’s a breach – it’s going to hurt.
For Small Business – This is secure and works efficiently:
For a lot of small businesses, the simplest and most makes sense setup is still the boring stuff that works: local area network, on-site data, and secure remote access. A well-built LAN is straightforward to understand, straightforward to secure, and straightforward to control.
Your data lives where you can point at it, your access paths are known, and you’re not stapling your business to everybody else’s tenants in the same giant ecosystem.
Yes, remote access is a solved problem. Proper VPN, locked-down accounts, least privilege, and basic hygiene. It’s not sexy, but neither is replacing business data after it gets vaporized.
Backups? This is where local really shines. You can back up on-site for fast restores and replicate off-site for real disaster recovery—two copies, two locations, same philosophy.
That whole setup is own able. You own the data, you own the recovery process, and you’re not waiting for someone else’s status page to decide whether your business gets to function today.
Your downtime is your problem either way, so you might as well, own it, and, design it so you can fix it.
With decent hygiene, redundancy, and tested backups, your business stays operational. When the internet goes out, because it will, you’re not sitting there staring at a login screen asking, “Where’s my stuff?” It’s still on your LAN, at your office, and you can still work.
Threat Math – Calculus:
There’s also a simple threat-math reason local can be safer: it’s decentralized.
When your business runs on your own infrastructure, you’re not sitting in a giant, labeled pile of targets.
The bad guys have to find you first. They have to footprint you, figure out what you are, probe your edge, and put in real work, and the ROI for them is not worth it.
That doesn’t make you invincible, but it absolutely changes the cost/benefit equation. Most criminals don’t want “hard.” They want scale.
They’d rather go after the big basket with all the eggs in it than spend their night hunting one small business that actually made them work.
Centralized is convenient, right up until it becomes catastrophic at scale. Or, put another way, centralization is great until you discover you’ve been living in the blast radius in a hacking group the whole time.
Why the Internet was built decentralized in the first place
Here’s the part most business owners don’t think about. The modern internet didn’t grow up with a “centralize everything” mindset.
Back in the early network days, researchers were thinking about survivability—what keeps working when parts of the network are damaged or down.
RAND Corporation work by Paul Baran explored distributed communications where a network keeps functioning even if nodes/links are lost—because there is no single “hit this and everything dies”.
Later, the design philosophy behind the ARPANET internet protocols emphasized survivability and avoiding fragile intermediate state—keep the network robust even when gateways fail.
That’s the fundamental difference:
- Centralized target: huge attack surface, huge reward, huge blast radius.
- Decentralized target: smaller cross-section per victim, more work to compromise broadly, failures are more contained.
“Put everything in one place, it’ll be simpler,” remember: simplicity and resilience are not the same thing.
Centralization:
In an on-prem world, an attacker has to find you, profile you, and break your specific environment. That takes a lot of effort and luck.
In the cloud world, the game shifts. Attackers don’t need to love your business. They just need to love your identity layer and your configuration habits.
Because once they learn a pattern—credential theft, token abuse, OAuth consent tricks, weak admin controls, risky tenant defaults—they can scale it across thousands of organizations that all “live in the same apartment complex.”
Cloud doesn’t make you the only target. It can make you one unit in a massive high-rise where the bad guys already have the blueprint.
The business model for Microsoft and other companies
Back in the day, reality looked different. Bandwidth was smaller. Remote apps were clunky. So, businesses ran domain controllers, file servers, and email on-prem because that’s what worked.
But now the pipes are fat, browsers are fast, and cloud services are mature enough that the old model (sell you software once) turns into a better business model, sell you services forever, Software as a service, SaaS.
Let’s not pretend the incentives don’t exist. Companies benefit when customers move from one-time licensing and local infrastructure into subscription ecosystems like Microsoft 365 and Azure. The roadmap follows the money.
The marketing follows the roadmap.
“Companies want you to do it” does not automatically mean “it’s safer.”
It’s just different risk—shifted into identity, configuration, and concentration.
Microsoft is explicit about that shared responsibility boundary: in the cloud, you still own your identities and data security, and your responsibilities vary by service type.
If your org migrates to cloud, and nobody tightens identity, permissions, conditional access, device posture, and backup strategy… you didn’t modernize. You just moved the mess.
Does Big provider mean no incidents
This is where people get hypnotized by the curtain: “It’s Microsoft—surely it’s secure.
Microsoft has publicly disclosed major nation-state incidents, including the 2024 Midnight Blizzard intrusion into Microsoft corporate email accounts.
Microsoft also documented the Storm-0558 incident, where forged tokens were used to access cloud email for a limited set of organizations.
“The Storm-0558 hack carried out on Microsoft revealed in July was thought to be limited to Outlook.com and Exchange online. But in a recent revelation, researchers at the cloud security startup Wiz have detailed a larger, more insidious aspect of a hack on Microsoft’s M365 platform.” Citation is Here:
This is not “Microsoft is unsafe.” This is, “the basket is valuable, and therefore it gets attacked.”
If you centralize your business operations into a single control plane and assume that means you can stop thinking about resilience, you’re betting the company on a faulty assumption.
Cloud is cheaper because we’re a small Business
Small businesses don’t go cloud because they’re dumb. They go cloud because they think they have limited funds and limited staff, and cloud looks like the smart answer.
- “I can’t afford servers.”
- “I can’t manage infrastructure.”
- “I don’t have an IT department.”
Fair, however here’s what most small businesses miss. You don’t need an IT department to have reliable infrastructure, and you don’t need stacks of money to build resilience.
A solid small-business infrastructure isn’t a data center. It’s a modern design:
- Proper perimeter security
- Patch management that actually happens
- Endpoint protection
- Identity controls that aren’t optional
- Backups that are recoverable, not just “successful”
- A design that doesn’t hinge on one fragile box that can take the whole operation down
If you don’t have the capability to manage that internally, good. You shouldn’t. That’s why competent, Managed Service Providers, MSPs exist.
Anti-Concentration design:
If you want cloud benefits without cloud fragility, you design like and, assume failure to reduce the harm to your business.
Here’s what that looks like, in plain English.
1. Identity hardening – Identity is the new perimeter:
- MFA that can’t be bypassed with “text me a code and I’m done”
- Conditional access that blocks risky sign-ins
- Least-privilege admin
The cloud loves identity. Attackers love identity. So, you harden identity first.
2. Independent backups – Sync is not a backup:
If it’s only synced, it can sync disasters too: deletions, crypto-encryption, permissions wreckage, and damn I deleted it moments.
You want independent, restorable copies with tested recovery, not a comforting green check mark.
3. An egress plan, Can I get my stuff back:
This is the part almost nobody does until it’s too late.
An egress plan answers four questions:
- How do I get my data out if I have to?
- How long will it take at my bandwidth and my data size?
- What will it cost (tools, labor, possible vendor fees)?
- Who owns the steps when things are on fire?
If you can’t answer those questions, you’re not “cloud-first.” You’re vendor-locked by accident.
4. Operational fallback – What happens when the cloud has a bad day?
What do you do if email, files, or collaboration tools are down today?
- Can staff still work?
- Can you still invoice?
- Can you still run payroll?
- Can you still serve customers?
When payroll is due, and the system dies, the machine doesn’t care that it was “a bad time.” It didn’t get the memo, and the bill always comes due, with payment, penalties, and pain.
Homes:
Homeowners are small businesses now:
- Remote work.
- Side hustles
- Taxes
- Family photos
- School documents
- Financial records.
The same centralized assumption shows up at home, “I put it in the cloud, so I’m safe.”
No. You put it in the cloud, so it’s convenient. Safety still depends on identity security and independent backups. A home doesn’t need enterprise gear. It needs the same philosophy:
- Protect the account
- Keep separate copies
- Assume failure
- Keep the blast radius small
Conclusion:
Reason Everyone’s Going Cloud: The LAN Networking Skill that Is quietly disappearing:
One reason the world is going cloud, the people who know how to build and run clean on-prem networks are aging out, and the training pipeline isn’t replacing them at the same rate, and Microsoft does not want to.
The old Microsoft certification world that minted “server people” got retired, and the emphasis shifted hard toward cloud and hybrid roles. That doesn’t mean on-prem is dead, and it doesn’t mean Microsoft can’t teach it.
However, the center of gravity is obvious: Microsoft wants workloads in Microsoft’s ecosystem, because that’s where the subscription revenue and platform control lives.
So, small businesses look at local infrastructure and think, “We can’t do that anymore,” when what they really mean is, “We don’t know anyone who can do it confidently.”
That’s the part that should make business owners pause. Businesses get pushed toward one way of doing things because the other way becomes, a great mystery of how things used to be done. “What was that long thick cable used for anyways.”
Over time, the old-school ability to design simple, resilient LANs—on-site data, sane segmentation, and secure remote access. It might become either something fewer and fewer people can do confidently, or a premium skill that becomes more valuable precisely because fewer people can do it well.
When businesses remember what they’re actually buying. Control, resilience, and a smaller target profile, they start to see the security value in keeping the crown jewels on-site and making attackers hunt for you.
That doesn’t mean a local network can’t be breached. It can. But it’s usually harder, higher-effort, and a much lower ROI. The bad guys have to find you, footprint you, work through layers, and keep access without getting caught.
Most criminals don’t want “hard”—they want scale. Make it enough work, and they’ll move on to the big, centralized basket that practically comes with a welcome mat.
Sincerely,
Rick Arnold – Arnold Consulting
Bio-Note:
When I’m not running Arnold Consulting, I also have an Etsy shop called Vintage Uranium Vault, where I document antique crystal and glass and re-home pieces to buyers who appreciate a craft that is not coming back.
Especially the increasingly rare art of making and cutting leaded crystal. If you’re hunting a unique gift—or a piece for your office that looks sharp and starts conversations.
Browse the shop here: [https://www.etsy.com/shop/VintageUraniumVault?ref=lp_mys_mfts Thanks for taking a look!
Rick Arnold – Arnold Consulting